漏洞描述
開發中文件上傳功能很常見,作為開發者,在完成功能的基礎上我們一般也要做好安全防護。
文件處理一般包含兩項功能,用戶上傳和展示文件,如上傳頭像。
文件上傳攻擊示例
upload.php
<?php
$uploaddir = 'uploads/';
$uploadfile = $uploaddir . basename($_FILES['userfile']['name']);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploadfile)){
echo "File is valid, and was successfully uploaded.\n";
}
else {
echo "File uploading failed.\n";
}
?>
upload.html
<form name="upload" action="upload1.php" method="POST" ENCTYPE="multipart/formdata"> Select the file to upload: <input type="file" name="userfile"> <input type="submit" name="upload" value="upload"> </form>
上述代碼未經過任何驗證,惡意用戶可以上傳php文件,代碼如下
<?php eval($_GET['command']);?>
惡意用戶可以通過訪問 如http://server/uploads/shell.php?command=phpinfo(); 來執行遠程命令
Content-type驗證
upload.php
<?php
if($_FILES['userfile']['type'] != "image/gif") {//獲取Http請求頭信息中ContentType
echo "Sorry, we only allow uploading GIF images";
exit;
}
$uploaddir = 'uploads/';
$uploadfile = $uploaddir.basename($_FILES['userfile']['name']);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploadfile)){
echo "File is valid, and was successfully uploaded.\n";
} else {
echo "File uploading failed.\n";
}
?>
該方式是通過Http請求頭信息進行驗證,可通過修改Content-type ==> image/jpg繞過驗證,可以通過腳本或BurpSuite、fiddle修改
如下
Content-Disposition: form-data; name="userfile"; filename="shell.php"
Content-Type: image/gif
圖片類型驗證
該方法通過讀取文件頭中文件類型信息,獲取文件類型
備注:如JPEG/JPG文件頭標識為FFD8

upload.php
<?php
$imageinfo = getimagesize($_FILES['userfile']['tmp_name']);
if($imageinfo['mime'] != 'image/gif' && $imageinfo['mime'] != 'image/jpeg') {
echo "Sorry, we only accept GIF and JPEG images\n";
exit;
}
$uploaddir = 'uploads/';
$uploadfile = $uploaddir . basename($_FILES['userfile']['name']);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploadfile)){
echo "File is valid, and was successfully uploaded.\n";
} else {
echo "File uploading failed.\n";
}
?>
可以通過圖片添加注釋來繞過此驗證。
如添加注釋<?php phpinfo(); ?>,保存圖片後將其擴展名改為php,則可成功上傳。
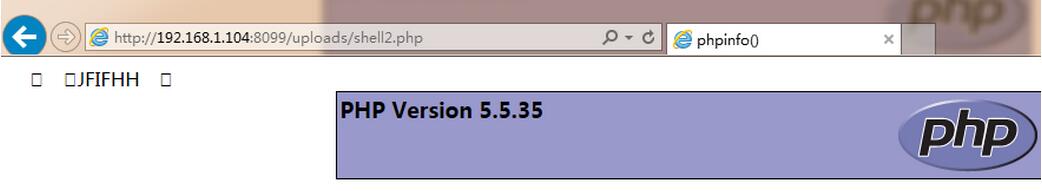
上傳成功後訪問該文件則可看到如下顯示
文件擴展名驗證
通過黑名單或白名單對文件擴展名進行過濾,如下代碼
upload.php
<?php
$blacklist = array(".php", ".phtml", ".php3", ".php4");
foreach ($blacklist as $item) {
if(preg_match("/$item\$/i", $_FILES['userfile']['name'])) {
echo "We do not allow uploading PHP files\n";
exit;
}
}
$uploaddir = 'uploads/';
$uploadfile = $uploaddir . basename($_FILES['userfile']['name']);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploadfile)){
echo "File is valid, and was successfully uploaded.\n";
} else {
echo "File uploading failed.\n";
}
?>
當黑名單不全,構造特殊文件名可以繞過擴展名驗證
直接訪問上傳的文件
將上傳文件保存在非web root下其他文件夾下,可以防止用戶通過路徑直接訪問到文件。
upload.php
<?php
$uploaddir = 'd:/uploads/';
$uploadfile = $uploaddir . basename($_FILES['userfile']['name']);
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploadfile)) {
echo "File is valid, and was successfully uploaded.\n";
} else {
echo "File uploading failed.\n";
}
?>
用戶不可以直接通過http://localhost/uploads/ 來訪問文件,必須通過view.php來訪問
view.php
<?php $uploaddir = 'd:/uploads/'; $name = $_GET['name']; readfile($uploaddir.$name); ?>
查看文件代碼未驗證文件名,用戶可以通過例如http://localhost/view.php?name=..//php/upload.php,查看指定的文件
解決漏洞示例
upload.php
<?php
require_once 'DB.php';
$uploaddir = 'D:/uploads/';
$uploadfile = tempnam($uploaddir, "upload_");
if (move_uploaded_file($_FILES['userfile']['tmp_name'], $uploadfile)) {
$db =& DB::connect("mysql://username:password@localhost/database");
if(PEAR::isError($db)) {
unlink($uploadfile);
die "Error connecting to the database";
}
$res = $db->query("INSERT INTO uploads SET name=?, original_name=?,mime_type=?",
array(basename($uploadfile,basename($_FILES['userfile']['name']),$_FILES['userfile']['type']));
if(PEAR::isError($res)) {
unlink($uploadfile);
die "Error saving data to the database. The file was not uploaded";
}
$id = $db->getOne('SELECT LAST_INSERT_ID() FROM uploads');
echo "File is valid, and was successfully uploaded. You can view it <a href=\"view.php?id=$id\">here</a>\n";
} else {
echo "File uploading failed.\n";
}
?>
view.php
<?php
require_once 'DB.php';
$uploaddir = 'D:/uploads/';
$id = $_GET['id'];
if(!is_numeric($id)) {
die("File id must be numeric");
}
$db =& DB::connect("mysql://root@localhost/db");
if(PEAR::isError($db)) {
die("Error connecting to the database");
}
$file = $db->getRow('SELECT name, mime_type FROM uploads WHERE id=?',array($id), DB_FETCHMODE_ASSOC);
if(PEAR::isError($file)) {
die("Error fetching data from the database");
}
if(is_null($file) || count($file)==0) {
die("File not found");
}
header("Content-Type: " . $file['mime_type']);
readfile($uploaddir.$file['name']);
?>
上述代碼文件名隨機更改,文件被存儲在web root之外,用戶通過id在數據庫中查詢文件名,讀取文件,可以有效的阻止上述漏洞發生
總結
通過以上示例分析,可總結一下幾點
1.文件名修改,不使用用戶上傳的文件名
2.用戶不可以通過上傳路徑直接訪問文件
3.文件查看采用數據庫獲取文件名,從而在相應文件服務器讀取文件
4.文件上傳限制文件大小,個人上傳數量等
以上就是本文的全部內容,希望對大家的學習有所幫助,也希望大家多多支持。